Information Assurance and Security
About Course
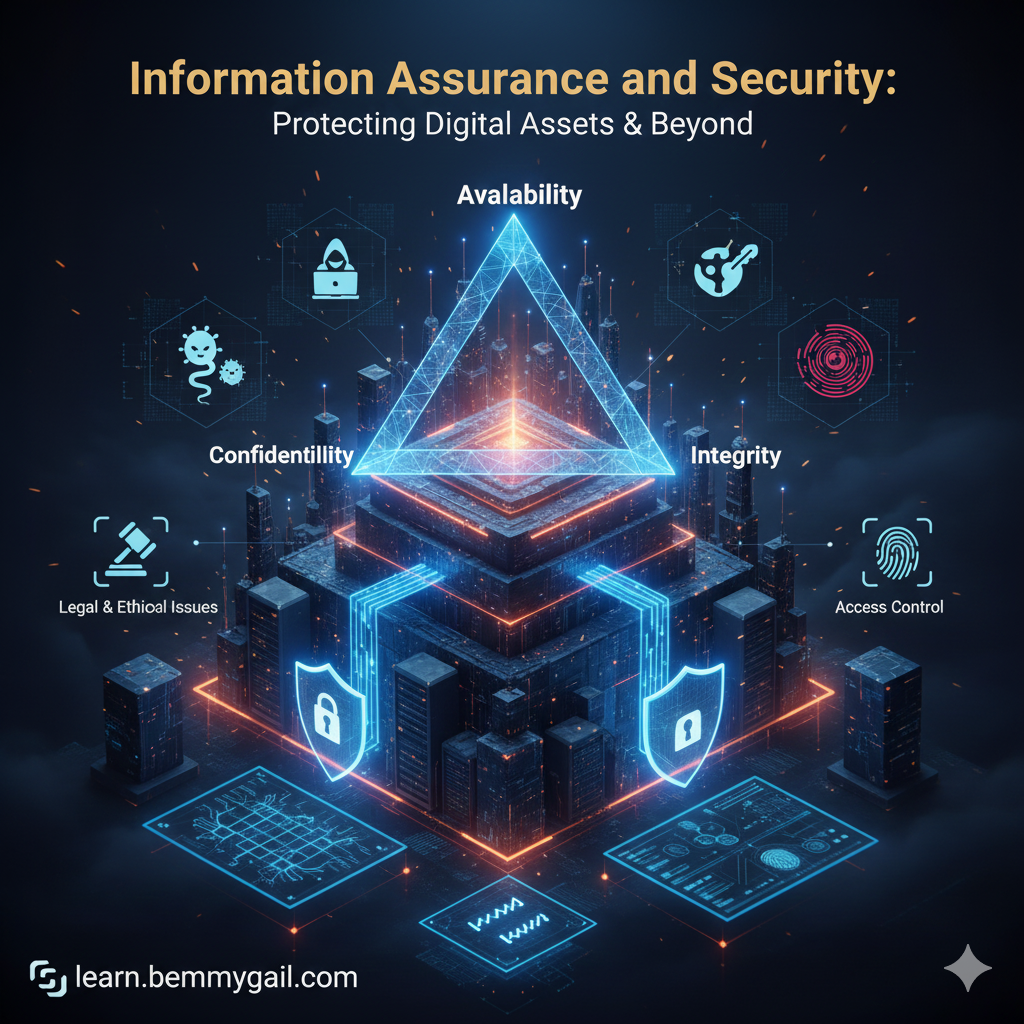
Information Assurance and Security: Protecting Digital Assets & Beyond
This course introduces the foundational principles of Information Assurance and Security (IAS), centered on the CIA Triad (Confidentiality, Integrity, Availability). Students will explore the evolving landscape of cyber threats, vulnerabilities, and attacks, alongside the critical legal, ethical, and professional issues in information security. Essential domains like risk management, access control, cryptography, and physical security are covered, equipping students with the core knowledge to safeguard digital information in any organizational context.
Course Content
Module 1: Foundations and Threats
-
Introduction to Information Security & The CIA Triad
04:07 -
Information Security & CIA Triad Quiz
-
Threats, Attacks, and Vulnerabilities
05:45 -
Quiz: Threats, Attacks, and Vulnerabilities
-
Preliminary Examination
Module 2: Legal, Ethical, and Risk Management
Module 3: Access Control and Cryptography
Module 4: Practical Security Measures
Earn a certificate
Add this certificate to your resume to demonstrate your skills & increase your chances of getting noticed.
Student Ratings & Reviews